Introduction
CISOs face mounting pressure from ransomware attacks, data breaches, operational disruptions, and regulatory scrutiny. The average cost of a data breach in the United States surged past $10 million in 2025, driven by regulatory penalties and extended detection times.
Response speed and coordination now determine whether an incident becomes a minor disruption or a catastrophic failure. The right platform makes the difference.
Choosing an incident management platform requires evaluation beyond technical capabilities. You must assess:
- Compliance alignment with frameworks like NIST and FEMA NIMS
- Integration with your existing security stack
- Support for cross-functional teams spanning security, IT operations, legal, and executive stakeholders
This strategic decision shapes your organization's resilience in the face of evolving threats.
TL;DR
- Modern platforms detect, coordinate, document, and resolve security incidents in real-time
- Top solutions integrate with SIEM/EDR/SOAR tools and support NIST, FEMA NIMS, and ISO 27001 compliance
- Selection criteria should prioritize real-time alerting, automated workflows, cross-departmental collaboration, and comprehensive audit trails
- Organizations using AI and automation in security operations saved $1.9 million on average compared to those without automation
- Compare 10 platforms designed for compliance, seamless integration, and enterprise-scale security operations
Overview of Incident Management Platforms for CISOs
CISOs face mounting pressure to respond faster to security incidents while maintaining comprehensive documentation for compliance. Incident management platforms provide the centralized systems needed to detect, coordinate, and resolve security incidents in real time.
These platforms serve as the operational backbone for responding to cyber threats, IT disruptions, and physical security incidents across the organization.
Traditional manual incident tracking through spreadsheets and email chains creates dangerous visibility gaps and compliance risks. The mean time to identify and contain a breach dropped to 241 days in 2025—a nine-year low—but remains dangerously high.
Modern platforms address this through continuous monitoring, automated response workflows, and comprehensive audit trails essential for regulatory compliance and board reporting.
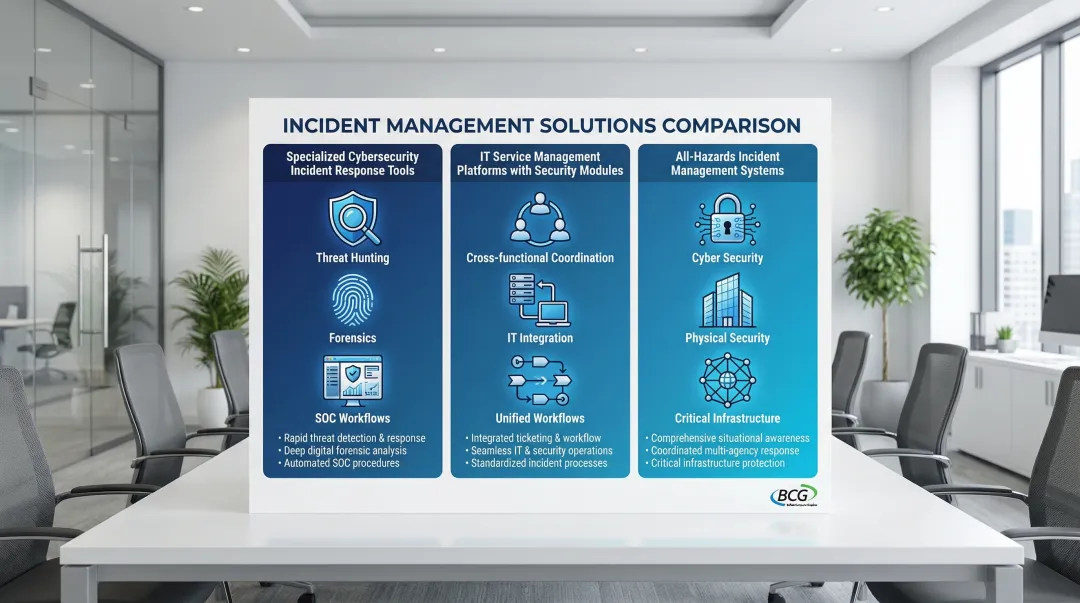
The incident management platform market offers CISOs three primary categories:
- Specialized cybersecurity incident response tools — Focused on threat hunting, forensics, and security operations center (SOC) workflows
- IT service management platforms with security modules — Enable cross-functional coordination between IT and security teams
- All-hazards incident management systems — Support both cyber and physical security incidents across enterprise, government, and critical infrastructure
10 Essential Incident Management Platforms for CISOs
The platforms below were selected based on CISO-specific criteria: regulatory compliance support, integration capabilities with security tools, real-time alerting and automation, audit readiness, scalability for enterprise environments, and proven track record in handling high-stakes incidents.
PagerDuty
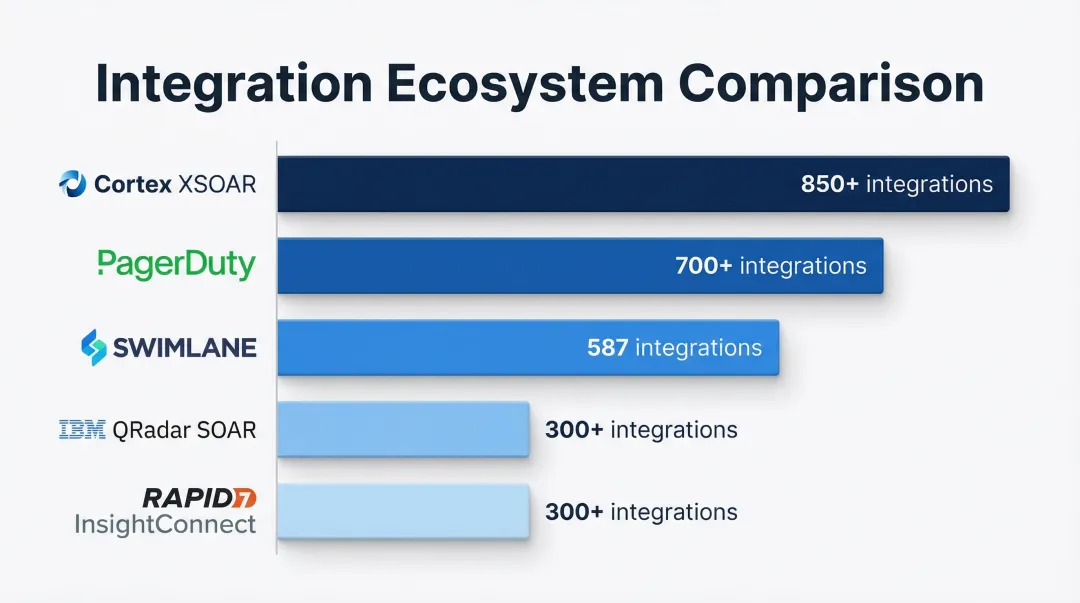
PagerDuty began as an IT operations platform but has evolved into a leading incident response solution widely adopted by security teams. The platform offers real-time alerting, sophisticated on-call scheduling, and integration with 700+ tools in the security and IT stack, making it a highly connected hub for security operations.
For CISOs, PagerDuty's standout capability is AI-powered event intelligence that correlates related alerts, dramatically reducing alert fatigue. The platform's integration ecosystem connects seamlessly with SIEM and SOAR platforms, enabling data flow across your security stack.
Comprehensive analytics support post-incident review and continuous improvement, helping you demonstrate operational maturity to the board.
| Aspect | Details |
|---|---|
| Key Strengths | Real-time incident alerting and escalation, AI-driven event correlation, 700+ integrations including major SIEM/SOAR platforms |
| Best For | Enterprise security teams needing rapid incident mobilization, organizations with complex on-call rotations, teams seeking to reduce alert fatigue |
| Compliance Support | SOC 2 Type II certified, supports audit trail requirements, integrates with compliance monitoring tools |
ServiceNow Security Incident Response
ServiceNow is a comprehensive IT service management platform with a robust security incident response module. Its enterprise adoption, workflow automation capabilities, and tight integration with IT operations enable coordinated response across security and infrastructure teams.
The unified platform bridges IT and security incident management, enabling the cross-functional coordination essential for complex incidents. Vulnerability response workflows connect threat detection directly to remediation.
Advanced reporting capabilities support board-level communication, while proven scalability in large enterprise environments makes it suitable for Fortune 500 deployments.
| Aspect | Details |
|---|---|
| Key Strengths | Unified ITSM and security incident management, sophisticated workflow automation, enterprise-grade scalability and reporting |
| Best For | Large enterprises needing coordination between security and IT ops teams, organizations requiring extensive customization, CISOs seeking unified platform for multiple use cases |
| Compliance Support | Supports NIST, ISO 27001, GDPR compliance workflows, comprehensive audit trails, built-in compliance reporting templates |
Splunk Enterprise Security (ES)
Splunk ES is a leading SIEM platform with integrated incident response capabilities. Named a Leader in the 2024 Gartner Magic Quadrant for SIEM for the tenth consecutive time, Splunk offers powerful data analytics, threat intelligence integration, and the ability to correlate security events across hybrid and multi-cloud environments.
Industry-leading analytics and visualization capabilities enable deep forensic investigation, while extensive threat intelligence integration supports proactive threat hunting.
The mature ecosystem of 1,700+ curated detections aligned to industry frameworks lets you build comprehensive security operations centers with customized detection logic.
| Aspect | Details |
|---|---|
| Key Strengths | Advanced SIEM with incident response workflows, powerful analytics and threat hunting, extensive security app ecosystem |
| Best For | Organizations with mature security operations centers, teams requiring deep forensic analysis capabilities, environments generating high volumes of security telemetry |
| Compliance Support | Pre-built compliance dashboards for major frameworks (PCI DSS, HIPAA, SOC 2), supports evidence collection for audits, regulatory reporting capabilities |
IBM Resilient (IBM Security QRadar SOAR)
IBM Resilient is a leading SOAR platform now integrated with QRadar SIEM. It focuses on security orchestration, automated response playbooks, and case management capabilities that help security teams coordinate complex incident response activities across 300+ enterprise-grade integrations.
The mature playbook library for common attack scenarios reduces response time significantly. Strong threat intelligence integration provides context for decision-making, while comprehensive case management tracks incidents from detection through resolution.
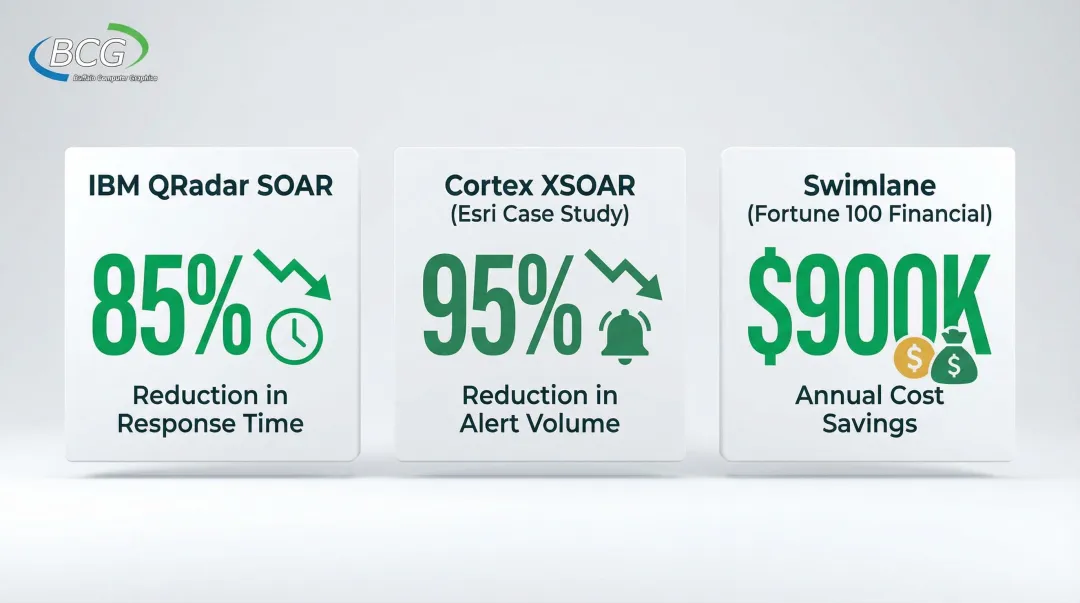
IBM's extensive security research backing delivers cutting-edge threat intelligence. Clients have reported 85% reduction in incident response time.
| Aspect | Details |
|---|---|
| Key Strengths | Advanced SOAR capabilities with 300+ integrations, comprehensive playbook library, strong case management and documentation |
| Best For | Organizations seeking to automate repetitive security tasks, teams handling high incident volumes, enterprises requiring sophisticated orchestration across security tools |
| Compliance Support | Automated evidence collection for compliance, supports regulatory reporting requirements, integrates with GRC platforms |

Palo Alto Networks Cortex XSOAR
Cortex XSOAR is Palo Alto Networks' security orchestration platform built on the Demisto acquisition. It focuses on automating the entire incident lifecycle from detection through remediation with the industry's largest SOAR ecosystem of 850+ integrations and collaborative investigation workspaces.
Industry-leading automation capabilities can reduce incident response time by up to 95%, as demonstrated by Esri's case study showing reduction from 10,000 to 500 weekly alerts. Collaborative investigation workspaces improve team coordination during complex incidents.
The extensive content pack library with pre-built playbooks for common threats accelerates deployment, while tight integration with Palo Alto's security ecosystem provides unified visibility.
| Aspect | Details |
|---|---|
| Key Strengths | Industry-leading automation and orchestration, 850+ integrations, collaborative incident workspaces with war room functionality |
| Best For | Organizations seeking maximum automation of security operations, teams coordinating complex multi-stakeholder investigations, Palo Alto Networks customers |
| Compliance Support | Automated compliance workflows, supports audit documentation requirements, integrates with major GRC platforms |
Microsoft Sentinel
Microsoft Sentinel is a cloud-native SIEM and SOAR platform tightly integrated with Azure and Microsoft 365 environments. It offers AI-powered analytics, serverless architecture that scales automatically, and native integration with Microsoft security tools, making it particularly attractive for Microsoft-centric organizations.
Seamless integration with the Microsoft ecosystem (Azure, M365, Defender) eliminates integration overhead, while AI and machine learning capabilities enhance threat detection accuracy.
The cost-effective pay-as-you-go pricing model with commitment tiers offering up to 52% savings provides budget flexibility. Strong support for hybrid cloud environments aligns with most enterprises' infrastructure reality.
| Aspect | Details |
|---|---|
| Key Strengths | Cloud-native SIEM/SOAR, native Microsoft ecosystem integration, AI-powered analytics, flexible consumption-based pricing |
| Best For | Microsoft-centric organizations, cloud-first enterprises, teams seeking scalable SIEM without infrastructure management overhead |
| Compliance Support | Built-in compliance workbooks for major frameworks, supports Azure compliance certifications, automated evidence collection from Microsoft services |
Buffalo Computer Graphics DisasterLAN (DLAN)
BCG's DisasterLAN is an all-hazards incident management system with over 20 years of proven performance in government, military, healthcare, and critical infrastructure sectors. DLAN is the first and only incident management system evaluated by FEMA's NIMS STEP program as fully compliant with NIMS and ICS principles, making it essential for organizations requiring federal compliance.
DLAN's unique all-hazards approach supports both cybersecurity and physical security incidents through a unified platform. FEMA NIMS compliance is critical for government agencies and contractors, while flexible deployment options (cloud or on-premise) address sensitive data requirements.
Template-guided Incident Action Plans aligned with FEMA guidelines ensure standardized response. Bandwidth-based licensing provides cost predictability compared to per-seat pricing. ISO/IEC 27001:2013 certified with 300+ deployments across government, military, and healthcare.
| Aspect | Details |
|---|---|
| Key Strengths | FEMA NIMS STEP compliant (only platform with this certification), all-hazards incident management (cyber + physical + operational), ISO/IEC 27001:2013 certified, 300+ deployments across government/military/healthcare |
| Best For | Government agencies and contractors requiring FEMA NIMS compliance, healthcare systems managing both security and emergency incidents, critical infrastructure organizations, enterprises needing on-premise deployment for sensitive data |
| Compliance Support | FEMA NIMS and ICS principles compliance, ISO 27001 certified, supports HIPAA and government regulatory requirements, comprehensive audit trails and evidence collection |

Atlassian Jira Service Management
Jira Service Management is a widely adopted ITSM platform with incident management capabilities. Recognized as a Leader in the 2025 Forrester Wave for Enterprise Service Management Platforms, it offers flexibility, strong collaboration features, and an extensive app marketplace with 624 security and compliance apps.
Highly customizable workflows can be tailored to specific security team processes, while strong integration with development tools enables DevSecOps workflows that bridge security and engineering teams.
The extensive marketplace of security-focused plugins extends functionality. Cost-effective pricing makes it accessible for mid-market organizations seeking enterprise capabilities without enterprise budgets.
| Aspect | Details |
|---|---|
| Key Strengths | Highly customizable workflows, strong collaboration features, extensive app marketplace, cost-effective for mid-market |
| Best For | Organizations already using Atlassian ecosystem, teams needing customizable incident workflows, mid-market companies seeking cost-effective solutions |
| Compliance Support | Customizable compliance workflows, audit trail capabilities, integrates with security and compliance plugins from marketplace |
Rapid7 InsightConnect
Rapid7 InsightConnect is a security orchestration and automation platform tightly integrated with Rapid7's vulnerability management and threat detection tools. It emphasizes automating security workflows and reducing manual tasks for security analysts through 300+ plugins for diverse IT and security system integrations.
Seamless integration with Rapid7's InsightVM and InsightIDR platforms provides unified vulnerability and incident management. Pre-built workflows for common security operations tasks accelerate deployment.
The user-friendly workflow builder doesn't require extensive coding knowledge, enabling security teams to build automation independently. Strong focus on reducing mean time to respond (MTTR) through automated remediation steps.
| Aspect | Details |
|---|---|
| Key Strengths | Native integration with Rapid7 security tools, user-friendly automation workflow builder, pre-built security workflows, focused on reducing MTTR |
| Best For | Rapid7 customers seeking integrated automation, teams with limited automation expertise, organizations prioritizing quick time-to-value for orchestration |
| Compliance Support | Supports automated compliance workflows, integrates with vulnerability management for risk-based prioritization, audit documentation capabilities |
Swimlane
Swimlane is a security automation platform focused on low-code security orchestration. It emphasizes a visual workflow builder, extensive integration library with 587 connectors and 1,830 playbooks, and empowering security teams to build custom automation without heavy reliance on engineering resources.
The low-code platform enables security teams to build and maintain automations independently, reducing dependency on engineering. Flexible deployment options including on-premise support sensitive environments.
Strong focus on metrics and reporting demonstrates SOC efficiency improvements to executive stakeholders. Case management capabilities unify incident tracking across multiple security tools. A Fortune 100 financial company reported saving $900,000 per year by automating security use cases with Swimlane.
| Aspect | Details |
|---|---|
| Key Strengths | Low-code security automation platform, visual workflow builder, flexible deployment (cloud/on-prem), strong metrics and reporting |
| Best For | Organizations seeking security team ownership of automation, teams requiring on-premise SOAR deployment, CISOs needing to demonstrate SOC efficiency metrics |
| Compliance Support | Automated compliance evidence collection, supports audit workflows, integrates with GRC platforms for unified risk management |
How We Evaluated These Platforms
We assessed platforms based on their ability to support the complete incident lifecycle as defined by frameworks like NIST and SANS: detection, triage, investigation, containment, eradication, recovery, and post-incident review.
This comprehensive approach ensures that selected platforms provide end-to-end capabilities rather than point solutions.
Key evaluation criteria included:
- Seamless integration with existing security stack (SIEM, EDR, threat intelligence, vulnerability management)
- Compliance and audit readiness supporting regulatory frameworks with evidence collection and reporting
- Automation and orchestration capabilities that reduce manual work and response time
- Documented performance in large, complex enterprise environments
Understanding these criteria helps avoid common selection mistakes. CISOs often stumble by:
- Over-prioritizing point solutions that don't integrate well with existing tools
- Focusing solely on features without considering team skill levels and change management
- Underestimating the importance of vendor stability and long-term support
- Failing to evaluate platforms against industry-specific compliance requirements
Key Selection Criteria for CISOs
Integration and Interoperability
The platform must integrate seamlessly with your existing security ecosystem including SIEM, EDR, firewalls, threat intelligence feeds, and vulnerability management tools.
Poor integration creates data silos, manual data transfer, and slower response times that undermine the platform's value.
Verified integration counts matter: Cortex XSOAR (850+), PagerDuty (700+), and Swimlane (587) offer extensive ecosystems that reduce custom coding requirements. Check whether your specific tools are supported before committing, as integration gaps can significantly impact deployment timelines and effectiveness.
Compliance and Regulatory Alignment
CISOs must ensure the platform supports specific regulatory requirements—HIPAA for healthcare, FEMA NIMS for government, SOC 2 for SaaS providers. Platforms lacking proper compliance features create audit failures and regulatory penalties.
The share of organizations paying regulatory fines greater than $50,000 increased by 22.7% in 2024, making compliance support non-negotiable. Prioritize platforms with automated evidence collection, comprehensive audit trails, and compliance reporting capabilities that align with your industry requirements.
Automation and Orchestration Capabilities
Automation is critical for modern incident response. Key benefits include:
- Reducing mean time to respond (MTTR)
- Eliminating manual repetitive tasks
- Ensuring consistent execution of response procedures
- Enabling teams to handle higher incident volumes without matching headcount increases
Real-world ROI demonstrates the value:
- IBM QRadar SOAR: 85% reduction in response time
- Cortex XSOAR: 95% reduction in alert volume for Esri
- Swimlane: $900k/year savings for a Fortune 100 financial company
Platforms should offer both pre-built playbooks for common scenarios and customization capabilities for organization-specific workflows.
Deployment Flexibility and Scalability
Platforms should support your deployment requirements (cloud, on-premise, or hybrid) based on data sensitivity and regulatory constraints.
Government and defense organizations often require on-premise deployment for classified data, while cloud-first enterprises benefit from serverless architectures.
The solution must can scale as your organization grows in size, complexity, and threat volume without requiring platform replacement. Organizations using AI and automation in security operations saved $1.9 million on average compared to those without, demonstrating the value of scalable automation capabilities.
Conclusion
Selecting an incident management platform is a strategic decision. It should align with your organization's specific risk profile, regulatory requirements, existing technology stack, and team capabilities—not just vendor marketing or analyst reports.
During your evaluation:
- Conduct proof-of-concept testing with real incident scenarios from your environment
- Involve key stakeholders including security analysts, IT operations, and compliance teams
- Assess vendor stability and long-term support capabilities
Recognize that incident management is mission-critical infrastructure requiring proven reliability.
Organizations requiring FEMA NIMS compliance or all-hazards capabilities supporting both cyber and physical security incidents should evaluate platforms with specialized certifications. BCG's DisasterLAN offers proven performance in government and critical infrastructure environments.
With ISO/IEC 27001:2013 certification and 300+ deployments across government, military, and healthcare sectors, DLAN provides the regulatory alignment and operational reliability essential for high-stakes incident response.
Frequently Asked Questions
Which is better, SIEM or SOAR?
SIEM focuses on collecting and analyzing security event data to detect threats, while SOAR automates response actions and coordinates incident workflows. Modern security operations typically need both capabilities through integrated platforms like Microsoft Sentinel and Splunk ES, or specialized tools that connect well.
Is Jira good for incident management?
Jira Service Management works well for incident management when properly configured, especially for organizations already using Atlassian tools. It may require security-specific plugins from its marketplace of 624 security apps to match purpose-built platforms, but offers cost-effective collaboration capabilities.
What features should CISOs prioritize in incident management platforms?
Priority features include real-time alerting and automated response to reduce MTTR, comprehensive integration with existing security tools, audit trail and compliance reporting for regulatory requirements, and collaboration tools that coordinate security, IT, and business teams during incidents.
How do incident management platforms integrate with existing security tools?
Platforms integrate through APIs, webhooks, and pre-built connectors enabling bi-directional data flow with SIEM, EDR, and other security tools. Integration quality varies—Cortex XSOAR (850+ integrations) and PagerDuty (700+ integrations) offer extensive ecosystems, so verify your specific tools are supported.
What is the difference between incident management and incident response platforms?
Incident response platforms focus specifically on cybersecurity incidents with features like threat hunting, forensic analysis, and malware containment. Incident management platforms take a broader approach supporting IT incidents, operational disruptions, and in some cases physical security incidents. Many organizations need both capabilities, which can be provided by integrated platforms or complementary specialized tools.
Do incident management platforms support compliance reporting for regulations like HIPAA and SOC 2?
Leading platforms include compliance reporting with pre-built templates for major frameworks, automated evidence collection, and audit trail capabilities. Compliance support varies, so verify your specific requirements are addressed—BCG's DLAN platform offers ISO 27001 certification and is the only system with FEMA NIMS STEP program compliance.