Security incident management systems provide the structured protocols and coordination tools organizations need to detect, respond to, and resolve security threats while maintaining compliance with frameworks like NIMS, ICS, and NIST standards. With Verizon's 2025 DBIR analyzing over 16,000 security incidents globally, the volume and complexity of threats make scalable, automated incident management essential.
This guide covers the top incident management tools serving both emergency management and IT security sectors, plus proven best practices for building effective incident response capabilities.
TLDR
- Incident management systems coordinate response teams and communications during security emergencies
- Choose between NIMS-compliant platforms for physical security or IT-focused tools for cyber incidents
- Organizations with tested incident response plans save an average of $1.49 million per breach through faster detection and containment
- Selection criteria should prioritize compliance requirements, integration capabilities, and proven deployment track record over brand recognition alone
Overview of Security Incident Management Systems in Modern Organizations
A security incident management system combines protocols, tools, and processes that help organizations detect, respond to, coordinate, and resolve security incidents or emergencies.
These systems provide structured methods to coordinate personnel, equipment, communications, and facilities during uncertain situations that threaten normal operations.
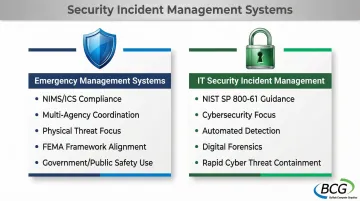
These systems fall into two distinct categories, each serving different organizational needs:
Emergency Management Systems follow NIMS (National Incident Management System) and ICS (Incident Command System) frameworks mandated by FEMA for government agencies, public safety organizations, hospitals, and utilities. These platforms coordinate multi-agency response to natural disasters, terrorism, and large-scale physical threats.
IT Security Incident Management platforms follow NIST SP 800-61 guidance, focusing specifically on cybersecurity threats like data breaches, malware, and system disruptions. These tools emphasize automated detection, digital forensics, and rapid containment of cyber threats.
The market reflects growing demand across both categories:
- MarketsandMarkets projects the cybersecurity market to reach $196.20 billion by 2030, as threat volumes and compliance requirements continue to expand
- Organizations using AI and automation in security operations reduce breach detection and response times by up to 102 days on average
- These improvements demonstrate measurable ROI from structured incident management capabilities
Top Security Incident Management Tools for Emergency Management and Security Operations
When evaluating incident management platforms, organizations need solutions that balance compliance requirements, proven reliability, and practical functionality. The following tools represent leading options across emergency management and security operations, each excelling in specific use cases.
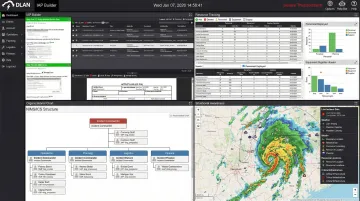
DisasterLAN (DLAN) by Buffalo Computer Graphics
Buffalo Computer Graphics brings 43 years of experience developing incident management solutions for emergency response coordination.
DLAN stands as the first and only incident management system evaluated by FEMA's NIMS STEP program as fully compliant with NIMS and ICS principles, making it the benchmark for government and public safety applications requiring verified compliance.
Why it stands out:
- Serves 300+ deployments across the U.S. and 10+ countries, including FEMA, U.S. Coast Guard, Department of Defense, and state/local agencies
- Provides template-guided Incident Action Plans aligned with FEMA guidelines, eliminating guesswork from emergency documentation
- Uses unique bandwidth-based licensing instead of per-seat pricing for flexible, cost-effective scaling
- Maintains ISO/IEC 27001:2013 certification for rigorous information security standards
| Category | Details |
|---|---|
| Key Features | NIMS/ICS compliant workflows, template-guided Incident Action Plans, multi-agency coordination tools, resource tracking, situational awareness dashboards |
| Deployment Options | Cloud or on-premises deployment with flexible licensing; used across local, county, state, tribal, regional, and territory levels |
| Best For | Emergency management agencies, public safety organizations, government entities, hospitals, utilities, and organizations requiring NIMS/ICS compliance |
ServiceNow Security Incident Response
ServiceNow leverages its position as an enterprise IT service management leader to deliver comprehensive security incident response capabilities for large organizations. Nearly 80% of the Fortune 500 rely on ServiceNow's platform-of-platforms approach, making it a natural choice for enterprises already invested in the ServiceNow ecosystem.
Why it stands out:
- AI-powered incident detection identifies threats before they escalate
- Extensive integration ecosystem connects security tools across the enterprise
- Robust workflow customization adapts to complex organizational structures
- Enterprise-scale performance handles high-volume incident loads without degradation
| Category | Details |
|---|---|
| Key Features | Automated workflows, incident tracking, threat intelligence integration, real-time collaboration, advanced analytics and reporting |
| Deployment Options | Cloud-based SaaS platform with enterprise-grade security and scalability |
| Best For | Large enterprises with complex IT environments, organizations needing IT and security incident management integration |
Opsgenie by Atlassian
Opsgenie focuses on alert management and on-call scheduling for DevOps and IT operations teams, with emphasis on real-time incident coordination. As part of the Atlassian ecosystem, it integrates seamlessly with Jira, Confluence, and other development tools teams already use.
Why it stands out: Opsgenie's multi-channel alerting ensures critical notifications reach responders via SMS, voice calls, email, and push notifications simultaneously. Intelligent alert routing directs incidents to the right team members based on skills, availability, and escalation policies. With 200+ monitoring tool integrations, the platform aggregates alerts from across your infrastructure. Mobile-first design enables rapid response from anywhere, critical for distributed teams maintaining 24/7 operations.
| Category | Details |
|---|---|
| Key Features | Alert aggregation and routing, on-call management, escalation policies, incident timelines, post-incident reporting |
| Deployment Options | Cloud-based with mobile apps for iOS and Android; integrates with Jira, Slack, AWS, and other DevOps tools |
| Best For | DevOps teams, IT operations, organizations with distributed on-call teams needing 24/7 incident response capabilities |
PagerDuty
PagerDuty positions itself as a digital operations management platform specializing in real-time incident response enhanced by AIOps capabilities. The platform has become synonymous with on-call management in technical operations, trusted by organizations managing complex digital services.
Why it stands out:
- Machine learning-powered event intelligence reduces alert noise by up to 91%, letting teams focus on genuine threats
- Automated response orchestration executes predefined workflows instantly when conditions trigger
- Comprehensive analytics track MTTA and MTTR for continuous improvement
- 700+ integrations connect monitoring, ticketing, and communication platforms
| Category | Details |
|---|---|
| Key Features | Event intelligence and correlation, automated response orchestration, real-time collaboration, status pages, post-incident analysis |
| Deployment Options | Cloud-based platform with mobile access; integrates with 700+ tools across monitoring, ticketing, and communication platforms |
| Best For | Technical teams managing digital services, organizations needing AIOps capabilities to reduce alert fatigue and improve response times |
Everbridge
Everbridge specializes in critical event management and mass notification for public safety, corporate security, and emergency management applications. The platform bridges physical and digital security, addressing threats ranging from natural disasters to active shooter situations.
Why it stands out:
- Trusted by 5,400+ enterprises and government agencies globally, including 8 of the 10 largest U.S. cities
- Reaches 650+ million people across 200+ countries and territories
- Multi-modal communication delivers notifications via SMS, voice, email, and mobile app simultaneously
- Location-based alerting targets specific geographic areas during emergencies
- Maintains FedRAMP Agency Authorization, ISO 27001, and SOC 2 compliance
| Category | Details |
|---|---|
| Key Features | Mass notification, critical event management, location tracking, threat assessment, two-way communication, audit trails |
| Deployment Options | Cloud-based platform with mobile apps; supports integration with existing emergency management systems and security operations centers |
| Best For | Public safety agencies, corporate security teams, healthcare organizations, utilities, and enterprises needing critical event management and mass notification |
Best Practices for Implementing Security Incident Management
Develop a Comprehensive Incident Management Plan
Create a detailed plan that includes clear definitions of incident types, severity levels, response procedures, and escalation protocols. Align your plan with relevant frameworks—NIMS/ICS for emergency management or NIST SP 800-61 for cybersecurity.
Organizations without formal plans pay 58% more per breach, making documentation essential rather than optional. Your plan should define:
- Incident classification criteria (what constitutes a minor vs. major incident)
- Severity level thresholds and corresponding response requirements
- Step-by-step response procedures for common incident types
- Clear escalation paths when incidents exceed initial response capabilities
- Communication protocols for internal teams and external stakeholders
Establish a Dedicated Incident Response Team
Build a team with clearly defined roles and responsibilities. Include representation from IT/security, operations, legal, communications, and executive management to ensure comprehensive coverage.
Ensure 24/7 availability through on-call rotations, particularly for organizations operating critical infrastructure or digital services. Key roles include:
- Incident Commander: Coordinates overall response and makes critical decisions
- Technical Lead: Directs technical investigation and containment activities
- Communications Lead: Manages internal and external communications
- Legal Advisor: Ensures compliance with notification requirements and preserves evidence
- Executive Liaison: Keeps leadership informed and secures necessary resources
Implement Regular Training and Exercises
Test your incident response procedures through tabletop exercises, simulations, and live drills. Organizations that test IR plans at least twice a year save an average of $1.49 million per breach, yet only 30% conduct regular tabletop exercises.
Use these exercises to:
- Identify gaps in procedures, tools, or team knowledge
- Practice coordination between different teams and departments
- Test communication channels under stress conditions
- Validate escalation procedures and decision-making authority
- Build muscle memory so teams respond instinctively during real incidents
Conduct Thorough Post-Incident Analysis
After every significant incident, identify root causes, document lessons learned, and implement improvements. NIST SP 800-61 emphasizes that lessons learned meetings are the most important—yet most often omitted—part of incident response.
Create a knowledge base of past incidents to inform future responses and reduce resolution times through:
- Detailed incident timelines documenting what happened and when
- Root cause analysis identifying why the incident occurred
- Assessment of what worked well and what needs improvement
- Specific action items with owners and deadlines
- Updates to runbooks and procedures based on new insights

How We Chose the Best Security Incident Management Tools
Our evaluation focused on five critical criteria:
- Compliance capabilities with NIMS/ICS, NIST, and ISO standards
- Proven deployment track records with government and enterprise clients
- Feature comprehensiveness for incident response workflows
- Integration options with existing security and IT systems
- Feedback from security and emergency management professionals
We prioritized platforms with documented success in high-stakes environments—FEMA disaster response operations and Fortune 500 cybersecurity centers. Compliance certification was essential, particularly FEMA NIMS STEP evaluation for emergency management tools and FedRAMP authorization for government deployments.
Common selection mistakes to avoid:
- Focusing solely on price rather than compliance and feature fit
- Overlooking integration needs with monitoring tools, communication platforms, and ITSM solutions
- Choosing tools that don't scale with organizational growth
- Ignoring industry-specific requirements like NIMS/ICS compliance for emergency management
Evaluate tools based on your specific operational requirements, not marketing promises or brand recognition alone.
Conclusion
Selecting the right security incident management tool depends on your organization's specific needs and regulatory environment. Emergency management agencies, hospitals, and utilities require NIMS/ICS compliance that platforms like DisasterLAN provide, while IT teams prioritize DevOps integrations and AIOps capabilities found in tools like PagerDuty and Opsgenie.
Evaluate tools based on:
- Compliance requirements aligned with your regulatory environment
- Integration capabilities with your existing technology stack
- Scalability to support organizational growth
- Proven deployment track records in your specific industry
The right platform reduces breach costs, accelerates response times, and provides the structured coordination essential during high-pressure incidents.
Organizations requiring NIMS/ICS compliant systems with proven performance in government and emergency management applications can benefit from Buffalo Computer Graphics' DisasterLAN, backed by 43 years of experience and recognition as the first FEMA NIMS STEP evaluated solution. Contact BCG at (716) 822-8668 or info@bcgeng.com to learn how DLAN can enhance your incident response capabilities.
Frequently Asked Questions
What is a security incident management system?
A security incident management system combines protocols, tools, and processes that help organizations detect, respond to, and resolve security incidents. It provides structured methods to coordinate personnel, equipment, and communications during emergencies that threaten normal operations.
What is an example of an ICS system?
DisasterLAN (DLAN) by Buffalo Computer Graphics is an ICS-compliant system used by FEMA, U.S. Coast Guard, and emergency management agencies nationwide. It's the only incident management system evaluated by FEMA's NIMS STEP program as fully compliant with NIMS and ICS principles.
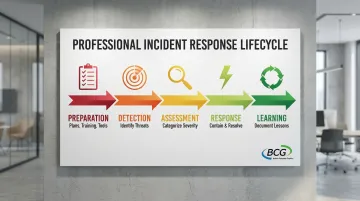
What are the 5 major components of an incident management system?
The five components are: Preparation (developing plans and training), Identification (detecting incidents), Assessment (categorizing by severity), Response (containing and resolving), and Monitoring and Learning (tracking effectiveness and documenting lessons).
How much do security incident management systems cost?
Cloud-based platforms typically charge $10-50 per user monthly for basic plans, with enterprise pricing for advanced features. Some systems like DisasterLAN use bandwidth-based licensing instead of per-seat pricing. Request quotes from multiple vendors to compare total cost of ownership.
What's the difference between NIMS and NIST incident management frameworks?
NIMS (National Incident Management System) is FEMA's framework for managing all types of incidents requiring multi-agency coordination—natural disasters, terrorism, large-scale emergencies. NIST SP 800-61 focuses specifically on computer security incident response for cybersecurity events like data breaches and malware. Organizations may need to follow both frameworks depending on their sector and incident types.
How long does it take to implement an incident management system?
Implementation takes 2-3 months for cloud-based platforms with standard configurations, or 6-12 months for complex on-premises deployments. Timeline depends on organizational size, integration needs, customization requirements, and whether you're migrating from an existing system.