Introduction: Why Your Incident Management RFP Needs a Strategic Checklist
When disasters strike, your incident management platform becomes mission-critical infrastructure. FEMA OIG audits revealed that inadequate IT systems forced response delays averaging 24 hours and contributed to $1.2 billion in increased recovery costs during major disasters.
These failures stemmed from non-integrated legacy systems that couldn't share data across agencies.
Selecting the right platform requires evaluating dozens of capabilities across functional, technical, compliance, and operational dimensions. Yet only 38% of state and local emergency management agencies use dedicated incident management platforms.
Most still rely on spreadsheets and email that fail under stress.
A structured evaluation framework solves this challenge. This comprehensive checklist provides the criteria used by emergency management agencies nationwide to evaluate vendors objectively, avoid costly mistakes, and ensure your platform performs when lives depend on it.
TLDR: Key Takeaways
- Functional capabilities, technical architecture, NIMS/ICS compliance, and security define platform quality
- Separate requirements as must-have versus nice-to-have to focus vendor responses and streamline evaluation
- Verify NIMS/ICS compliance through specific evidence—not all "incident management" software is built for emergency operations
- Your RFP should request real-world scenario evidence, interoperability standards, and multi-agency coordination examples
- Weighted scoring balances technical fit, compliance, deployment experience, and cost
Essential Functional Requirements for Incident Management Platforms
Functional requirements form the foundation of your evaluation—these capabilities determine whether your EOC staff and field personnel can execute their missions during incidents. According to DHS SAVER research, specific capabilities distinguish true emergency management platforms from generic incident tracking tools.
Incident Tracking and Documentation
Your platform must provide comprehensive incident logging with customizable fields for:
- Incident type, severity, location, and timeline tracking
- Resource assignments and personnel accountability
- Real-time updates accessible across desktop, mobile, and tablet devices
- Multimedia evidence attachment (photos, documents, maps, videos)
The system must maintain complete audit trails with version control and digital signatures for regulatory compliance.
DLAN exemplifies this approach with after-action reporting that's "ready by default," capturing decisions and actions as events unfold.
Resource Management and Deployment
Beyond tracking incidents themselves, your platform must manage the resources deployed to address them. Evaluate tools for tracking personnel, equipment, vehicles, supplies, and facilities in real-time:
- Resource requesting, allocation, and mutual aid coordination across agencies
- NIMS resource typing standards support (Type 1-5 classifications)
- Demobilization tracking and cost accounting
- Integration with GPS and RFID for asset location
DLAN's resource management capabilities have earned praise from public safety users who specifically value the ability to "manage and track resources at an incident and on blue-sky days."
Incident Action Planning (IAP)
Assess whether the platform provides template-guided IAP creation aligned with ICS forms:
- ICS-201: Incident Briefing with initial map and summary
- ICS-202: Incident Objectives for operational periods
- ICS-203: Organization Assignment for personnel
- ICS-209: Incident Status Summary (critical for state/federal reporting)
- ICS-214: Activity Log with chronological records for reimbursement
Verify collaborative IAP development with version control, approval workflows, and digital distribution. DLAN cuts IAP preparation time from hours to minutes through workflow-driven approvals and automatic version tracking.

Situational Awareness and Common Operating Picture
GIS and mapping capabilities should visualize incidents, resources, hazards, and critical infrastructure:
- Real-time data integration from weather services, traffic systems, and sensor networks
- Customizable dashboards for different roles (IC, EOC Director, PIO)
- Layer management for flood zones, evacuation routes, and shelter locations
- Streaming video integration from traffic and security cameras
Rochester Emergency Management transformed static flood-plain data into dynamic DLAN map layers during a major rain event, significantly improving decision-making and EOC coordination.
Communications and Notifications
Effective coordination requires robust communication capabilities. Built-in tools should support:
- Secure messaging between EOC staff, field personnel, and partner agencies
- Integration with mass notification systems for public warnings
- Multi-channel notifications (SMS, email, voice, mobile app push)
- Two-way communication for confirmation tracking
Technical Architecture and Integration Requirements
Technical architecture determines long-term platform viability, total cost of ownership, and integration with existing systems.
GAO designated federal IT acquisition as "High Risk" due to lack of disciplined practices—your RFP must address these concerns.
Deployment Model and Infrastructure
Specify your deployment preferences based on security policies, internet reliability, and budget:
Cloud-based (SaaS):
- Accessible if local EOC is compromised
- Requires FedRAMP authorization for federal agencies
- Must include data residency, redundancy, and disaster recovery
On-premise:
- Greater control but introduces single points of failure
- Needs robust COOP capabilities and off-site backups
Hybrid:
- Local redundancy with cloud backup
- Offline capabilities with automatic synchronization
Integration and Interoperability
Your RFP should require detailed API documentation and pre-built connectors for:
- CAD/911 systems for automatic incident creation
- GIS platforms (Esri ArcGIS, OGC-compliant services)
- Mass notification systems (IPAWS/CAP integration)
- Asset management and HR systems
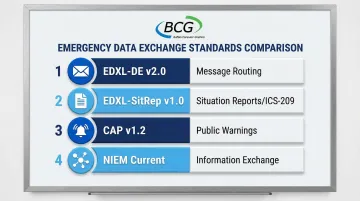
Evaluate support for emergency management interoperability standards:
| Standard | Version | Purpose |
|---|---|---|
| EDXL-DE | v2.0 | Container for routing emergency messages |
| EDXL-SitRep | v1.0 | Standardized situation reports (ICS-209) |
| CAP | v1.2 | Common Alerting Protocol for public warnings |
| NIEM | Current | National Information Exchange Model |
Look for platforms with built-in data transform capabilities that support custom integrations without extensive development. BCG's DLAN system, for instance, includes an XML data transform engine that enables cost-effective integration with these standards.
Performance, Scalability, and Reliability
Establishing clear performance benchmarks ensures vendors provide concrete commitments:
- Uptime: 99.9% to 100% availability required 24/7
- Concurrent Users: Scalability to support surge operations (2,000+ users)
- Response Times: Maximum acceptable latency under peak load
- Historical Performance: Request vendor uptime data from past 12 months
Mobile and Field Access
Evaluate native mobile apps for iOS and Android:
- Offline capabilities for areas with limited connectivity
- Incident reporting, resource status updates, photo/video capture
- IAP access and real-time situational awareness
- Automatic data synchronization when connectivity restores
User Experience and Accessibility
Emergency management staff should be able to use the system without extensive IT training:
- Intuitive interface for users with varying technical skill levels
- WCAG 2.1 AA accessibility standards compliance
- Customization of workflows, forms, and terminology without custom development
- Role-based permissions with automatic refresh capabilities
Compliance, Security, and Standards Requirements
Incident management platforms handle sensitive data and must meet strict security and compliance standards. NIST SP 800-53 Rev 5 provides the gold standard for security controls.
NIMS and ICS Compliance
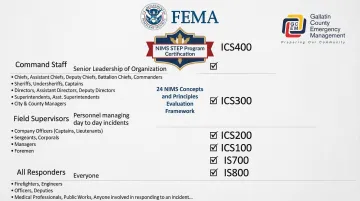
Require vendors to demonstrate how their platform supports NIMS principles:
- ICS organizational structure and role-based workflows
- Resource typing aligned with FEMA standards
- IAP templates matching official ICS forms
- Scalability from single-agency to multi-jurisdictional incidents
Critical Benchmark: In October 2010, DisasterLAN became the first and only incident management system evaluated by FEMA's NIMS STEP program as fully compliant with all 24 NIMS concepts and principles.
This certification provides unprecedented assurance of federal standards compliance—use this as your benchmark when evaluating vendor claims.
Security and Data Protection
Demand detailed security architecture documentation covering:
- Encryption standards (data at rest and in transit)
- Authentication methods (SSO, SAML 2.0, Active Directory integration)
- Role-based access controls and audit logging
- ISO 27001 or SOC 2 Type II certification
Look for vendors with proven security credentials. Buffalo Computer Graphics holds ISO/IEC 27001:2013 certification, demonstrating mature security practices. DLAN supports federated identity providers, ADFS, Shibboleth 2.0, and LDAP-based services.
Regulatory and Legal Compliance
Beyond security architecture, verify the platform meets regulatory requirements specific to your organization.
Specify applicable regulations:
- CJIS: Required for law enforcement integration
- HIPAA: Required for healthcare incidents and patient tracking
- FISMA: Required for federal agencies
- Business Associate Agreements: Required for protected health information
Assess data retention policies, audit logging capabilities, and e-discovery support to ensure compliance during investigations.
Business Continuity and Disaster Recovery
Evaluate vendor resilience—will they remain operational during disasters?
- Documentation of backup procedures and geographic redundancy
- Recovery Time Objectives (RTO) and Recovery Point Objectives (RPO)
- Business continuity plans and financial stability indicators
Training and NIMS Certification Support
Verify whether the platform:
- Tracks personnel certifications (ICS-100, 200, 300, 400)
- Provides training materials aligned with ICS principles
- Generates reports on personnel qualifications for grant reporting
Vendor Qualifications and Experience Evaluation
Emergency management domain expertise distinguishes qualified vendors from generic software providers. Require:
Company Background:
- Years in business and financial stability
- Customer retention rates and deployment count
- References from similar organizations in government, utilities, and healthcare
Domain Expertise:
- Understanding of ICS, NIMS, EOC operations, and regulatory environment
- Staff with relevant certifications and emergency management experience
- Case studies demonstrating successful implementations
Support Model:
- Hours of operation (24/7 for mission-critical systems)
- Response time SLAs and escalation procedures
- Dedicated account management availability
These qualifications separate vendors with genuine emergency management depth from those offering generic software solutions.
Buffalo Computer Graphics brings 43 years of experience with 300+ deployments across the U.S. and customers in 10+ countries. Their team holds ICS training through the 400 level, with subject matter experts including Fire, EMS, and Emergency Managers experienced in both field and EOC operations.
Evaluation Framework and Scoring Methodology
A weighted scoring system prevents low-cost, low-capability vendors from winning critical safety contracts. Start by assigning point values that reflect your organization's priorities:
Recommended Weights:
- Functional Capabilities: 35% (core features, NIMS compliance)
- Compliance and Security: 25% (standards, certifications, architecture)
- Vendor Qualifications: 20% (experience, references, support)
- Cost: 15% (total cost of ownership)
- Implementation Approach: 5% (timeline, methodology, training)
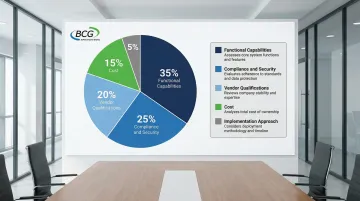
Requirements Classification
Build a requirements matrix that categorizes each capability:
- Mandatory: Vendor must meet to qualify for evaluation
- Highly Desired: Missing features result in significant point deductions
- Preferred: Nice-to-have capabilities that provide minor scoring advantages
Evaluation Team Structure
Assemble a cross-functional committee that includes:
- EOC management and emergency management director
- IT director, GIS specialist, and CISO
- Procurement officer and end users from operations
This mix ensures technical feasibility, operational fit, and compliance alignment are all evaluated.
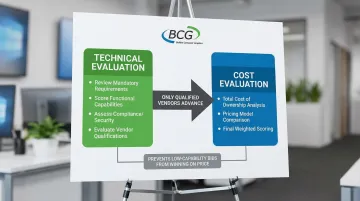
Two-Stage Review Process
Conduct technical evaluation first, scoring all qualified vendors against your weighted criteria. Only vendors meeting mandatory requirements move to cost evaluation, preventing low-capability bids from winning on price alone.
Implementation, Training, and Support Requirements
A clear implementation roadmap protects your agency from scope creep and ensures accountability. Define expected timeline milestones in your RFP to evaluate vendor readiness and project management capabilities:
- Discovery and requirements validation
- System configuration and customization
- Data migration from legacy systems
- Integration development and testing
- User training and exercises
- Go-live and transition support
Training quality directly impacts user adoption and system effectiveness. Specify your training requirements to assess vendor capabilities and avoid hidden costs:
- Number of users to be trained by role
- Preferred formats (on-site, virtual, recorded)
- Ongoing training support for new staff
- Exercise support for HSEEP-compliant drills
Long-term support determines total cost of ownership and system reliability during actual incidents. Request comprehensive support plans that address:
- Warranty period coverage and bug fix response times (critical vs. non-critical)
- Software update frequency, deployment process, and advance notice requirements
- Long-term maintenance contracts, upgrade paths, and version support lifecycle
Pricing and Commercial Terms Considerations
When evaluating incident management platforms, demand complete pricing transparency upfront to avoid hidden costs later.
Request comprehensive pricing breakdown:
- Software licenses (per-user vs. bandwidth-based vs. enterprise)
- Implementation services and configuration
- Training costs (initial and recurring)
- Annual maintenance and support fees
- Optional modules and add-ons
Alternative Licensing Models: Some vendors offer bandwidth-based pricing instead of per-user fees. BCG's approach, for example, charges based on system usage rather than user count, providing cost advantages for agencies with dramatic staffing fluctuations during activations.
This model eliminates paying for peak capacity licenses that sit unused during normal operations.
Require 3-year and 5-year total cost of ownership projections including:
- All recurring costs and anticipated upgrades
- Integration and customization expenses
- Training and support requirements
- Infrastructure and hosting costs
Frequently Asked Questions
What's the difference between an incident management platform and a mass notification system?
Incident management platforms handle the full incident lifecycle (planning, response, coordination, documentation), while mass notification systems focus solely on alerting the public via SMS, email, and voice. Most organizations need both, and integration between systems—like NY-ALERT and DLAN—enables coordinated emergency communication.
How do I evaluate NIMS/ICS compliance in vendor proposals?
Request ICS-compliant organizational charts, IAP templates matching official ICS forms, and resource typing aligned with NIMS standards. Third-party validation like FEMA NIMS STEP certification (which evaluates all 24 NIMS concepts) provides the most reliable compliance verification.
Should I prioritize cloud-based or on-premise deployment?
Cloud provides scalability and access from anywhere (critical if your EOC is compromised), while on-premise offers greater control for strict security requirements. Consider your internet reliability, security policies, and whether a hybrid approach with local redundancy fits your disaster recovery plan.
What are the most commonly overlooked requirements in incident management RFPs?
Key overlooked items include mobile offline capabilities, multi-agency coordination workflows, CAD/GIS integration, long-term data archiving, training/certification tracking, and interoperability standards (EDXL, CAP, NIEM). Also critical: vendor business continuity plans proving they'll remain operational during disasters.
How long does a typical incident management platform implementation take?
Straightforward implementations take 3-6 months, while complex deployments with extensive integrations require 6-12 months. Beware of unrealistically short timelines—proven implementations like Toronto's DLAN deployment for the 2015 PanAm Games show realistic planning is essential.
What should I include in vendor demonstration requirements?
Require live demos (not pre-recorded) using realistic scenarios from your jurisdiction, with participation from actual end users. Vendors should demonstrate creating incidents, developing IAPs, coordinating mutual aid, generating reports, and showing mobile capabilities plus integration with your existing systems.